
When a new year begins, I always find myself curious about certain things. This time, my question was: What do you focus on when strengthening your defensive capabilities? Through the “cyber ninjas” community on LinkedIn, I posted a poll with the intention of creating this blog and fostering discussion on the topic. Here we go!
My recent survey on LinkedIn reaffirmed the importance of frameworks like MITRE ATT&CK and D3FEND in strengthening cybersecurity defenses. Companies are at different stages of adoption and interest, with some focusing on next-generation capabilities, while others concentrate on automation, orchestration, and artificial intelligence (AI). AI brings substantial value both defensively and offensively, despite the hype. We’ll delve more into that later.
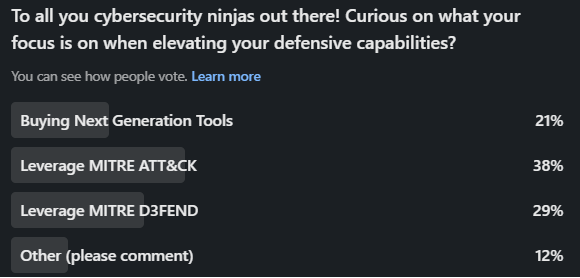
LinkedIn survey results.
Buying Next-Generation Tools:
Some of the feedback here was around improving secops with orchestration and automation. This is not surprising, as teams are lean and everyone is looking to streamline one’s operation to scale and level the playing field. Now, anyone who knows me understands that I am not a big fan of the “Next Generation” label being used in a product name, regardless of the vendor. The reason I am not interested in the title is that the label “Next Generation” never expires. In essence, a technology that entered the market 10 years ago as next generation may in fact not be as future-facing as we think. Unfortunately, everyone must use it or face the question of whether the product is, in fact, the next generation; ok, I digress. A couple of other items were brought to the surface in this category.
♦ Extended Detection Response to expand upon existing Endpoint Detection and Response capabilities with both Network Detection and Response as well as Identity Threat Detection and Response.
♦ Secure Services Edge to support hybrid workforces and move security to the cloud, allowing for consistent security control no matter where one is connecting from. Simplified access to services, removing the burden on the user regarding how they connect.
♦ Simplifying cloud-based controls with cloud-native capabilities that are cloud-agnostic, especially with hybrid cloud models.
♦ Shifting left, building security into the pipeline to reduce the risk once services are productionized, and maintaining security with every revision.
MITRE ATT&CK:
There is no surprise that this topped the list; however, I was a bit surprised that MITRE D3FEND was a close second. I do believe that an understanding of the adversary and their tactics and techniques elevates one’s defensive capabilities. Once you understand the details, you can determine how you match up with both prevention and detection-based capabilities, with detection being the absolute requirement. Assess the gaps and build out a strategy to address each item, improving your overall security posture. MITRE ATT&CK (Adversarial Tactics, Techniques, and Common Knowledge) is a knowledge base that provides a comprehensive framework for understanding the behavior of cyber adversaries. It categorizes and describes various tactics, techniques, and procedures (TTPs) used by attackers across different stages of the cyber kill chain. ATT&CK is widely used in cybersecurity to enhance threat intelligence, detection, and defense strategies. The below image is from MITRE ATT&CK Navigator and highlights capabilities from adversaries targeting finance.
MITRE D3FEND:
This one caught me off guard just a bit. I am fully aware of the framework and its value, but in my discussions with customers all over the world, it is not a topic of discussion that comes up in tandem with ATT&CK. There may be lots of reasons for that, but I am interested in learning more about real practical use cases where this has been applied. Ping me if you are willing to share your thoughts. So, what is MITRE D3FEND? D3FEND complements MITRE ATT&CK by focusing on providing a framework for defensive techniques. The D3FEND knowledge base aims to help organizations understand and implement strategies to defend against the tactics and techniques outlined in MITRE ATT&CK. It provides guidance on how to counteract and mitigate specific adversary actions, offering a more comprehensive approach to cybersecurity defense.
OTHER:
This is the catch-all bucket. The only comment I got here was a focus on AI from a couple of lenses. Good AI to combat evil AI—it’s a battle!
♦ Adding AI to the defensive arsenal will both combat AI-based threats from tools like FraudGPT that create very sophisticated emails to entice interaction and AI-infused malware to defeat our defensive capabilities. These AI tools have the guard rails removed, which prevents one from creating nefarious outcomes.
♦ Adding AI to the operational stack, which would make recommendations on policy and where best to apply such a control, finding the needle in a stack of needles with analyzing threats, to automating the change required to drive an outcome. All using natural language when interacting with the tool.
♦ Data is being shared using public-based AI tools. Having the ability to restrict access to these platforms to reduce company exposure, such as the data leak. We have seen this at large organizations, and many of them are building out controls to minimize the exposure. Just google it.
In the end, we are all at certain stages of the journey, and there is no perfect approach. Unfortunately, it falls in line with the famous IT phrase “it depends.”. If you have not considered a framework such as MITRE ATT&CK, then I would certainly put that on the list to help push your defensive capabilities towards the tactics the adversary will leverage against you.


