
APIC-EM: The Evolution From Traditional Management to SDN-led, Policy-based Automation
2 min read
The acronym SDN (Software Defined Networking) has been around for a while yet is still one of those concepts that mean different things to different people. At Cisco when we started the SDN journey for the Campus and Branch we asked our customers how SDN could benefit their networks. The answer to this question was that customers were looking for Simplification, Automation and Programmability.
APIC-EM stands for Application Policy Infrastructure Controller Enterprise Module and is the answer to these requirements in the Campus and Branch. With APIC-EM we are slowly transitioning from a traditional management approach to policy-based automation.
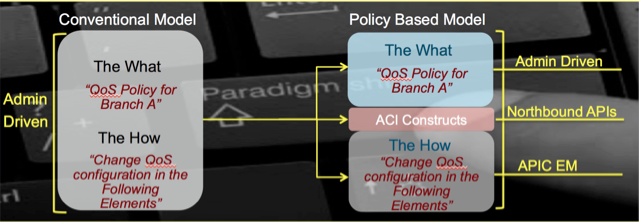
The goal of APIC-EM is to provide an abstraction to the complexity we experience today when deploying policies in our networks. Let’s provide an example to illustrate what is the difference between deploying policies in the traditional way compared to policy-based automation with APIC-EM.
Let’s say that we acquire a new Telepresence unit to be installed in our Branch A. From a business perspective, we want to ensure that Telepresence users in “Branch A” get the best video experience possible. After defining what we want to do (a.k.a. business policy), in the conventional model, network adminsitrators need to start thinking about how to make this happen. Network administrators need to figure out how to translate this business policy into network policy, that is, which devices need to be configured, what are the QoS capabilities of those network devices, what the correct synthax is and all other QoS-specific details.
In the new policy based model network administrators will only need to define their business policy allowing the controller to figure out all the implementation details for that policy. In this paradigm we are decoupling what we want to do from how this is going to be accomplished. In our previous example, the network administrator will still have to define the policy that will look something like this: “Telepresence traffic is a business critical application; Telepresence traffic is the most important video application in our network” and the controller will make all implementation decisions and act accordingly. The controller will decide things like which network devices need to be configured and what the exact synthax for the configuration is. The controller will then push this configuration to the appropriate network devices. This is how we are going to leverage abstraction and automation hence simplifying deployments.
The diagram below illustrates the difference between Conventional Model and Policy Based Model:
For more information on APIC-EM please visit our website.
 Lila Rousseaux has spent over twenty years in the Computer Networking industry in a variety of roles, from programming, implementation, design and architecture. In one of her first jobs, Lila had the opportunity to participate in the connection of the first Argentinian high speed link to the Internet as well as build the IP network connecting the 33 National Universities in Argentina.
Lila Rousseaux has spent over twenty years in the Computer Networking industry in a variety of roles, from programming, implementation, design and architecture. In one of her first jobs, Lila had the opportunity to participate in the connection of the first Argentinian high speed link to the Internet as well as build the IP network connecting the 33 National Universities in Argentina.
Lila Rousseaux is currently a Consulting Systems Engineer within the Enterprise Networking group based in Toronto, Canada. She joined Cisco Argentina in 1999 and moved to Canada in 2002. In her roles within Cisco, Lila has had the opportunity to work with a variety of customers: Service Providers, Enterprise, Partners and Commercial. Lila currently specializes in core routing & switching technologies and she is a Field Advisor for the Cisco routing and switching technology groups which allows her to provide feedback on strategy and direction of technologies and architectures. Education and knowledge transfer are a passion for Lila so she thoroughly enjoys speaking at events like Cisco Live and Cisco Connect.
She got her CCIE certification in 2001 and diligently re-certifies every two years! In addition, Lila holds a degree in Computer Science from the University of Buenos Aires.