
Some perfectly authentic looking web addresses are not what they seem, and not all browsers are taking the problem seriously.
Here is a challenge for you:
You clicked on a link in your email, and were routed to the website http://apple.com. The browser showed the green padlock icon, confirming that you had a secure connection. Often the word “Secure” is also shown besides the URL-window for extra reassurance. And yet, you were exposed to a successful phishing attack. Do you know how?
The answer is in the web address. It may look like it reads apple, but it is in fact a row of Cyrillic characters: A-Er-Er-Palochka-Ie. The security certificate is real enough, but all it confirms is that you have a secure connection to what you think is apple.com. It is not telling if you are connected to a legitimate site or not.
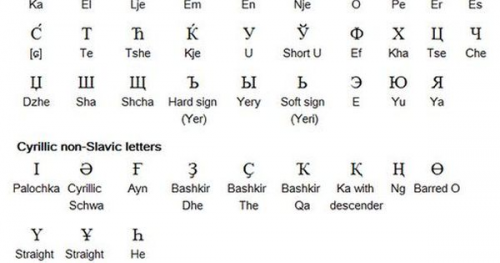
The proof-of-concept was demonstrated by the security researcher, Xundong Zheng, earlier this year. He wanted to highlight the problem with the way domain names can be registered and displayed. For a long time, domain names have only been registered with Latin characters, without special characters like æ, ø and å. But since 2003 we have actually had the possibility to use other alphabets like Cyrillic and Chinese.
This comes in handy if you want to register a domain name in Thai or Arabic characters, or just to correctly spell a web site in French or Icelandic.
Anything that can be represented with the Unicode-standard can be registered, even emojis. This opens an ocean of possibilities for misdirection, which hackers can exploit, by registering domains with characters from other alphabets that resembles Latin characters. Zheng writes:
From a security perspective, Unicode domains can be problematic because many Unicode characters are difficult to distinguish from common ASCII characters.
It is possible to register domains such as ‘xn--pple-43d.com’, which is equivalent to ‘аpple.com’. It may not be obvious at first glance, but ‘аpple.com’ uses the Cyrillic ‘а’ (U+0430) rather than the ASCII “a” (U+0041). This is known as a homograph attack (visual spoofing attack).
– Xudong Zheng
Some web browsers will expose these kinds of spoofing and rather show the underlying dodgy domain name. Other browsers don´t manage to uncover the trick and will show the Cyrillic domain name. These vulnerabilities in some web browser are now in the process of being fixed and updated by the vendors. The problem is that there will always pop up similar vulnerabilities in browsers and other applications, and phishing by getting the victim to end up at malicious domains, are one of our biggest challenges. Encrypting ransomware, stolen sensitive data, and the likes are typical negative effects of a phishing attack.
Cisco Umbrella – First Line of Defence
Everyone uses DNS (Domain Name Server) when we move around on the internet. Cisco Umbrella adds a security feature to the DNS service, which checks if the site you wish to access is trustworthy. Both the IP address and the URL name are checked for the domains you are on your way to access, and with Umbrella you stop the threats as far away from the users as possible.
Cisco Umbrella is perhaps the most effective defence against web-based threats, since the solution itself is cloud-based and uses big data analytics of 100 billion DNS look-ups every day, and analyses traffic from Cisco solutions worldwide. Large-scale machine learning is the only effective way to effectively stop attacks.