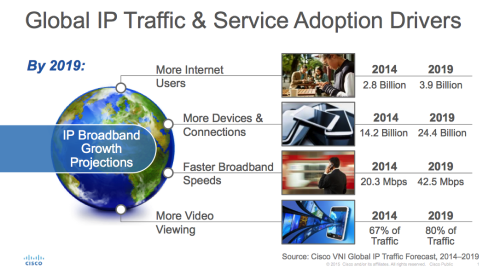
It sounds a bit of an oxymoron – Securing and Explosive. Indeed, security is what enables growth, actually, explosive growth in video delivered to multiscreen devices. Video viewing will make up 80% of global IP traffic by 2019, according to Cisco’s latest VNI report, and that traffic is expected to cross over 24 billion connected devices. This explosive growth of multi-screen IP video is expanding Pay-TV revenue opportunities. It is causing an intersection of Pay TV and OTT video, which is best protected by a combined CAS + DRM strategy to cover all devices on managed or unmanaged networks. But the story goes deeper than securing video content on the last mile.
Media broadcasters and service providers are also enhancing their operations to deliver IP video. They are migrating traditional private walled-garden head-ends to open, two-way IP-based head-ends that deliver interactive video services to all sorts of devices. This approach definitely keeps pace with growth, but it also creates new security threats – mal-ware, viruses, intrusions and hacks originating from the Internet. Content piracy can now happen right inside their premises, rather than just on the last mile. These sorts of cyber-attacks have been in the news recently, at media companies and service providers, coordinated and executed across continents. They have been draining balance sheets and occupying board room agenda with the question – “how do we protect our premium content at all ends?”
Cisco leads end-to-end security with the unified vision, strategy and solutions that fit the evolving service provider security needs. Cisco VideoGuard CAS and DRM solutions protect over $100 billion of Pay TV revenues on the last mile. But, our security capabilities extend end-to-end across the cloud video infrastructure, from content acquisition to video production and storage and onto distribution. Last week, at Cisco Live, we unveiled Cisco Firepower 9300, a carrier-class platform which extends our capabilities even further. Based on Cisco’s threat-centric approach, it is open and programmable, and extends to physical and virtual deployment models. For more information, please visit- www.cisco.com/go/spsecurity