For several years now I’ve been hoping that security companies and governments would get together in a federation against cyber attackers. Certainly, private security vendors selling network security products have cooperated to fight this growing menace.
Corporations and many individuals share enormous amounts of information and analytics on-line, to help thwart Cyber-attacks.
Cisco Talos, (Cisco’s Security Intelligence and Research Group), not only use their terabytes of web data, embedded agent feeds, and machine learning tools, to defend their customers against these threats, but  Cisco also subscribe to malware intelligence feeds from co-operating security vendors.
Cisco also subscribe to malware intelligence feeds from co-operating security vendors.
A third of small businesses in the UK are aware that they have been hacked, resulting in the loss their client’s personal client information, stolen and posted on-line, … and many have no plans or the resources to put Cyber Security defence in place.
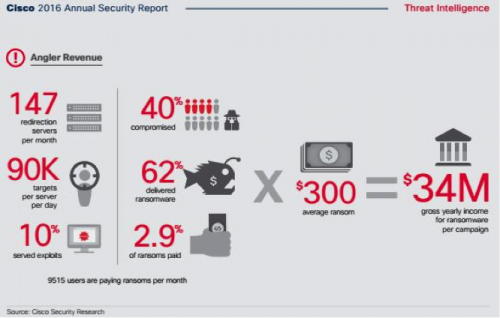
Government departments and major corporations are also enormously affected. Downtime of a week or more after a Crytolocker attack is not uncommon!
(From the Cisco 2016 Annual Security Report).
In the UK news as I blog today:
“The Ministry of Defence has revealed security was breached at RAF Shawbury, RAF Cosford, MoD Donnington, Copthorne Barracks in Shrewsbury, Nesscliffe Training Camp and Clive Barracks, near Market Drayton.”
and … “Qatar National Bank Suffers Massive Breach”
I believe we are at the point where the UK Government needs to step in and provide a Cyber Security as a free resource for the UK as a whole, setting an example for the world to follow. Cisco’s OpenDNS cloud security service could admirably fill this gap.
I eagerly read the Verizon 2016 Data Breach Report which was published online today, hoping to see a glimmer of industry cooperation. I was not entirely disappointed!
Over sixty corporations and several government institutions contributed to the Verizon 2016 DBR report (Data Breach Report), showing the level of cooperation we have in business today. Contribution companies ranged from Akamai to Wombat Security Technologies, and also included international government bodies such as the United Kingdom Computer Emergency Response Team (CERT-UK) and the US Secret Service.
So, if I could wave a magic wand and put the legislation in place for federated UK network security, I would mandate that broadband Service Providers be instructed to implement OpenDNS SaaS in their client-side network architecture as soon as possible. This feature would increase the service cost of individual broadband and mobile broadband services.
The public will of course react with a massive outcry against web censorship. However, if you consider how millions individual’s personal details and bank details have been touted on the Internet, there is nothing much private in that for them. Private individuals unknowingly send all their online browsing details back to the providers through the APPs they use on their tablets and Smart Phones, (Facebook, Google, Microsoft, games). There are websites where you can go to and see if your personal credentials are posted online somewhere! If you have a loyalty card, your personal online shopping details and home address details are at the mercy of your favourite retailer’s network security.
If you’re looking for a motive to qualify ISPs for including Cyber Security as a service, well, most attacks on corporations stem from an infected end point (around about 90%), so where would you begin putting security in place? We know that people don’t realise the security risk of not updating to the next new Java update, or new Flash player update, let alone operating system updates. Thank goodness Microsoft and Apple have automated their operating system updates.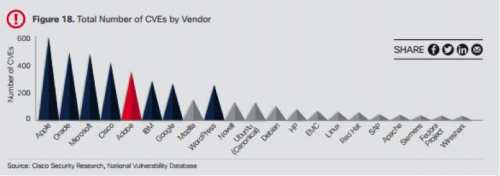
(CVEs are software vulnerabilities which are targeted by malware, installing Trojans)
Quoting here from the Verizon 2016 DBR, to save you the trouble of reading this excellent report right through at www.Verizon.com:
“To add another ray to this sunbeam, attackers are getting even quicker at compromising their victims” [after software vulnerabilities have been made public].
“Half of all exploitations happen between 10 and 100 days after the vulnerability is published, with the median around 30 days. This provides us with some general guidelines on which software vulnerabilities to prioritize along with some guidance on time-to-patch targets.”
“Phishing has continued to trend upward (like spawning salmon?) and is found
in the most opportunistic attacks as well as the sophisticated nation state
tomfoolery.”
“The bad news is, the detection deficit in Figure 8 is getting worse.” (see Verizon 2016 DBR).
So, I don’t want to be the bringer of bad tidings, but its evident that we are simply not winning the technology race as there are enormous profits to be made, and little risk to the threat actors hiding in foreign countries.
Antivirus products are absolutely necessary for endpoint protection, but there needs to be several additional security “shims” in place on endpoints such as Cisco AMP for large enterprises, Malwarebytes’ technology, CryptoPrevent, or sandboxing for home users, needed to cater for the dozens of un-patched vulnerabilities on the average corporate and private tablets and laptops. We can however to choose to move this security ‘shim’ into the Cloud. That is what OpenDNS enables, without anyone touching every single endpoint in the UK!
Here is an industry simile in the news right now: In a way, we could liken hackers to cold callers on the public telephone service. They phone, we don’t recognise the number, we pickup = we are ‘infected’. BT have introduced a service for the PSTN network called BT CallGuardian – and it stops cold callers dead! We need to do the same for the Internet!
So, if you read this blog and have any influence, TWEET for all ISPs to introduce Cisco OpenDNS cloud security as a mandatory service in their client’s broadband networks, home and business.
This will stop the cyber Threat Actors from making a mockery of our Digitization and IoT industry initiatives.
Tweet here: #OpenDNS4all