
Each year many security companies like Cisco Systems compile revealing Annual Security Reports.
These reports document the vast knowledge and experience that our malware researchers have accrued to thwart network attacks. This year, Cisco’s report shows the increasing industry collaboration between Cisco, OpenDNS and other threat research labs such as Level 3, to take down the bad actors. This is also true of many other security and network hardware vendors too.
The overall message within these Security Reports shows that malware writers, or bad actors as they are called, are ruthlessly attacking organisations to steal their customer’s credentials, and personal details, for profit. The sophistication of the technology that the malware operators use is as good as, and if not better, than the corporation they are targeting, who are trying to make an honest profit.
The professional bad actors are well funded, resilient, bold and coordinated. Moving rapidly to take advantage of both existing weaknesses in old end-of-support network infrastructure, and of the Corporation’s exposure when moving to a fully Digital Enterprise. Attackers now make extensive use of traffic encryption techniques, hiding the exfiltration of stolen data, and by using the most modern software development tools, and Cloud based hosting.
Security vendors are, as in years past, in a technology race against the Adversaries who are developing technologies and tactics that are growing in sophistication. Mostly these days its now all about how fast we as Defenders can detect and remediate from a single point of intrusion (from an Indication of Compromise) – but within hours, and not six months (the industry average). This is known as the Time to Detection (TTD). This view of attack continuum is promoted by Cisco’s as: BEFORE DURING and AFTER.
I would suggest that at this point you scan through the Cisco 2016 Annual Security Report here, and have a view of the YouTube video of our Cisco CEO and CSO discussing the ASR 2016 report contents.
https://www.youtube.com/watch?v=YFnAzZ23bBI
Okay your back, and I’m asking what is the reason that you are reading this Blog.
Are you looking for an answer to this ever growing security Risk?
Has your company already got around 35 security products installed and you’re still unsure, as many are, if your corporation is protected against asset theft and data manipulation?
You also have no idea of everything connected to the corporate network, and you’re not getting reports.
2/3rds of the respondents to the Cisco ASR2016 survey believe that their organisations are at risk from cyber security.
Cisco found that chief security officers (CSOs) and security operations (SecOps) managers are less confident that their security infrastructure is up to date, or that they are able to thwart attacks.
I’m going to briefly sketch out a few facts from the Cisco 2016 Annual Security report and then see if we can map out a route for your organisation to follow to install Integrated Threat Defense to guard against intrusions, both internal and external.
The biggest attack vector following the unpatched software vulnerabilities in Flash, Java and pdfs, are scams on Facebook and email phishing scams. This is where the attacks begin.
Cisco’s analysis of malware validated as “known bad” found that the majority of that malware, 91.3 percent, uses the Domain Name Service (DNS) to carry out campaigns. Cisco have uncovered “rogue” DNS resolvers in use on customer networks. The customers were not aware that the resolvers were being used by their employees as part of their DNS infrastructure. Failing to actively manage and monitor the use of DNS resolvers can result in malicious behaviour such as DNS cache poisoning and DNS redirection.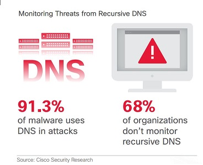
Cisco identified 115,000 devices in a one-day Internet test, scanning the Internet and then looking at these devices from the “outside in” (from the Internet view and into the Enterprises). Through Cisco’s scanning and analysis, Cisco found that 106,000 of the 115,000 devices had known vulnerabilities in the software they were running. That means 92 percent of the Cisco devices on this Internet sample were susceptible to known vulnerabilities.
According to Gartner, through 2018 more than 95 percent of firewall breaches will be caused by firewall misconfiguration.
So, its not surprising that in the UK that a relatively security conscious Service Provider got hacked by 15-year-old and that yet another Point of Sale terminal attack occurred at prominent world-wide hotel chain. This hotel chain has uncovered that most of their POS terminals world-over, had been hacked for the last 6 months, with POS devices continuously capturing and then exfiltrating customer credit card information to attackers since August 2015.
So, I think the most important first step you can take is to begin by primarily effectively securing the network and user devices against attack and then testing this on a regular basis by using an independent company – why?? – simple, because once you get into ‘remediation and forensics’ phase of an attack, its 100’s of times costlier than the protection phase, and you need special tools and skills, and your CEO will be interviewed on TV!
I attended a Cisco conference in August last year where there were 18,000 devices connected to the wireless infrastructure. The wireless network was being monitored by our Cisco Lancope product and it revealed that 39 personal devices connected to the wireless network had malware running on them. When back in my hotel room later that day I could see hack attempts from the hotel wireless network (managed by a 3rd party company).
 Do you have a problem convincing management that something needs to be done about security, or is your organisation living in a bubble of assumed safety?
Do you have a problem convincing management that something needs to be done about security, or is your organisation living in a bubble of assumed safety?
Where is the best place to begin to update your company’s security strategy, you may be asking?
Should you invite in 3 or 4 security vendors, evaluate their products, and then choose the company you think has the best cyber defence, remediation appliances, and software?
If you take this route you are very likely going to really undecided as where exactly to begin installing/changing what! … and your career might be on the line if you choose unwisely!
Here is my only assumption. I do not believe that the majority of enterprises have the resources to maintain their security strategy in-house. I qualify this by saying that if we could see, for example, the 600 employees working at Cisco TALOS security research and development labs and their professional qualifications, you would realise that few individuals working in commercial enterprise environment have the opportunity, certifications, and resourses to implement enterprise cyber threat defence solutions, without professional help.
If I was to put a number to this I would go as far as saying over 89% of enterprises, small and medium businesses do not, and cannot, have the required skills because of several factors – cost, staff availability, and staying abreast of the threat landscape.
It might have been possible 10 years or longer ago, but not today.
There are however two things and enterprise can do to secure their digital businesses:
What’s helping:
Many organisations are standardising on professional Security Standards. Organizations are following Standardized Information Security Policy Practice such as ISO 27001
Secondly, begin by getting in the security professionals like Portcullis, in the UK, to do a security audit of the inside and outside networks. Portcullis will run a security scan of all the user devices, network switches, and servers in your network. Since Portcullis are now a Cisco company they can also point out all the Cisco devices in your network which are either End of Support, or have unpatched firmware.
Portcullis will highly likely point out several recommend changes to the network such as ‘much finer segmentation of the network’, not only server segmentation in the Data Centre, buy segmenting each user from the others (Cisco TrustSec). Please see here for a report.
Many companies are now choosing to disconnect strategic work-stations and servers from the Internet.
Portcullis will also recommend logging of all network events and traffic flows (Cisco NetFlow), to make forensics possible.
Portcullis will also point out how important it is to know exactly what is connected to the corporate network, visibility, and how each device was authenticated (Cisco ISE).
Implementing the use of automation (Cisco Lancope) and coordination aspects of an integrated threat defence also help to reduce the time to detection, containment, and remediation.
To avoid the user misconfiguration aspect noted above by Gartner, consider moving to ACI/APIC orchestration, as soon and possible (SDN), beginning in the DC and moving on to the Enterprise LAN and WAN, described here.
Initially, this will generate a mountain of work for the enterprise’s security and network department but your efforts will pay off in the end by primarily reducing the attack surface within your organisation.
Please see Twitter #CiscoASR
1/3rd of successful attacks against organisations begin with a stolen password!
It only takes 2 seconds to brute force most passwords!
1 Comments
Every weekend i used to visit this site, because i want enjoyment, for the reason that this this web page conations actually fastidious funny stuff too.