
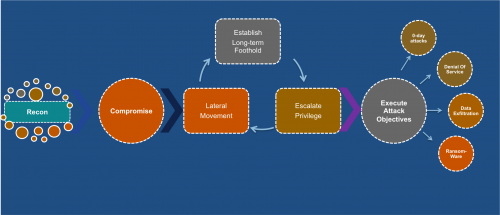
Security in the enterprise in a key requirement for running businesses today – it’s become a boardroom conversation in many companies. The recent increase in the rate and the severity of cyber-attacks has forced organizations across the board to rethink their security strategy and ensure data security at the highest levels. Almost 43% of all global companies have been experienced a breach and close to 66% take months or sometime even up to a year to recognize that they have been breached. We have seen many high profile attacks in recent times, the impact of which is profound – major sites going down because of DDoS attacks, customer credit and debit card information being stolen, millions of email accounts being swiped, insiders hacking and accessing sensitive information, and so on. It’s become extremely important for the network to be aware of the kill chain, and to intercept and secure the enterprise network.
Securing the Enterprise:
The CIOs and CISOs are entrusted with devising a robust security strategy that can deal with significant risks posed by an evolving threat landscape. Investments in secure capabilities are critical to address the challenges. It is important to ensure that solutions they invest in evolve when the risks multiply. The network can, and should play a very clear and important role in security the enterprise. The network should defend not just itself from attacks, but should secure the host to which is provides connectivity and services, the applications servers and the customer sensitive data that transits the network.
Recent trends in the enterprise have resulted in new threat vectors and new means for threats to enter the network.
• BYOD – Close to 60% of enterprises have already adopted BYOD, and another 14% are in the process of enabling the support. If you combine this with the fact that will be 50 billion connected devices by the year 2020, it becomes very clear that we have a clear and present danger that originates from within the enterprise. With the increase in number of unknown devices that will now enter the enterprise network, the number of threat variations also increases.
• IoT is the other trend that will result in significantly increased number of potentially unknown devices connecting to the network that could increase the threat level. The recent attack on Dyn is a clear proof point of this.
• Threats that originate from within the enterprise propagate in both north-south and east-west direction. While traditional firewalls are places at points in the network that would help detection of malicious traffic in the north-south direction, there is no mechanism in place to detect threat that spread laterally in the network.
• User malicious intent has been the cause of some of the attacks as in the case of AT&T. This is yet another critical source of threats in the enterprise.
The network is the entity that ties together the user, application and the devices. It would therefore need to play a role in securing the enterprise that can no longer be quantified as best-effort – it would have play both defense and offence in the new threat landscape.

